Your Outlook client is equipped with numerous security features that help you to deal with malicious programs such as viruses, worms, spyware, and phishing. And, Outlook follows different methods to fight against each of these malign programs. This article contains some essential security tips to manage Outlook securely.
Safe Handling of Attachments
Some attachments are more likely to contain suspicious files. For example, .vbs, .js, .exe, .bat etc. Outlook blocks these attachments by default. If your Outlook blocks any attachment, your infoBar will contain the list of blocked file types. While previewing, Outlook disables most of the embedded content in attachments including ActiveX controls, macros, scripts and so on.
Try to send an attachment in your Outlook that has file extension in the blocked list. You’ll see a warning message as shown in below
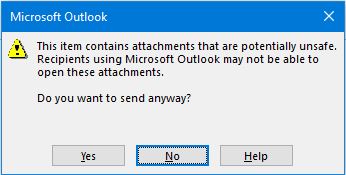
Anyhow, you can send the message – but at your own risk.
Dealing with Macro Viruses
There are powerful VBA macros that can run many commands on your PC. For the same reason, these VBA macros are considered to be a potential security threat. A hacker can exploit this through a document that if opened, a macro may execute allows spreading the virus on your PC.
From Microsoft Office 2010, Office Trust Center helps to guard against dangerous macros.
Protection against Phishing Attacks and Spam Emails
Phishing is one of the top followed malicious practices in the cyber world. Sometimes, it’s very hard to choose between a legitimate email and a phishing email. Outlook’s junk email filter carefully examines each of the incoming messages to separate suspicious and non-suspicious emails. If a mail is found suspicious, it’ll be sent to Junk E-mail folder. And, most of the functionalities including reply, reply all, etc. will be disabled for that message. Moreover, any attachments in that suspicious message will be blocked.
Note: If you your junk filter does not work or seems unresponsive, there are ways to rectify it.
Like phishing attacks, if a message was detected by Outlook as Spam, it’ll move to Junk E-mail folder. And, it’s very important because there could be chances for your mailbox be flooded with spam emails. Besides this, Outlook has an additional anti-spam filter. Sometimes, junk email senders use “web beacons” to collect your email address. When you open the message, the mail content will be downloaded to your PC and it verifies your email address. Then, your email address can be sold to more spammers resulting in more spam messages in your mailbox
Outlook anti-spam filter avoids “automatic picture downloads” in Outlook. If you’re sure that the email is from a trustworthy source, you can manually unblock pictures in that email.